Overview
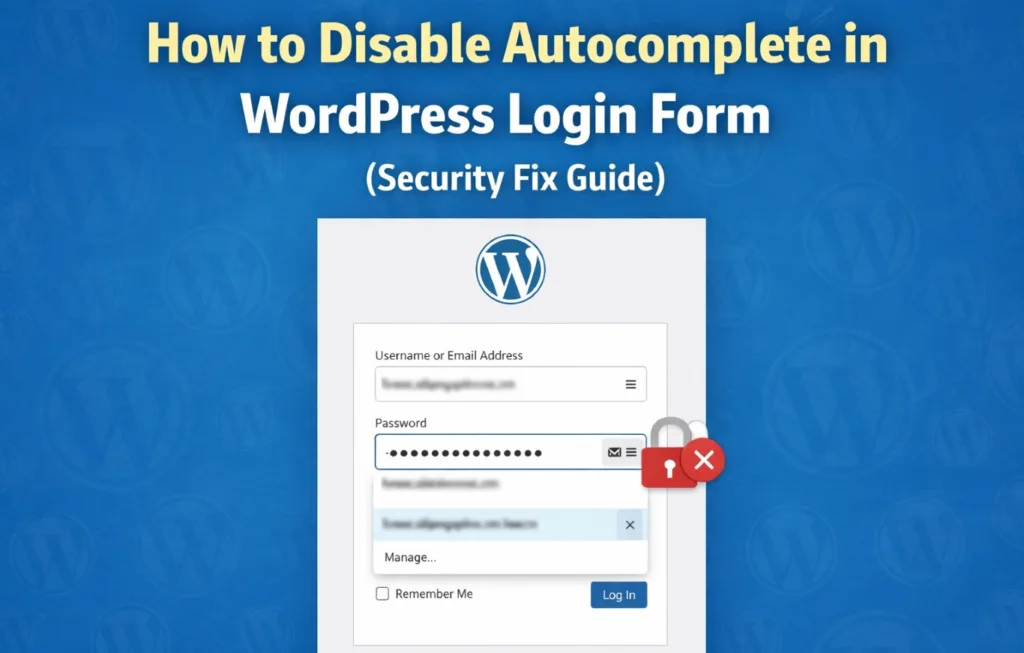
During a recent enterprise-level security audit conducted using Invicti, a vulnerability was identified related to the improper handling of browser autocomplete on a WordPress login form. The affected system was part of a high-security environment hosted under a .house.gov infrastructure, requiring strict compliance with web application security standards. This article outlines the issue, associated risks, and the remediation steps implemented to mitigate the vulnerability.
Vulnerability Details
- Type: Sensitive Data Exposure via Autocomplete
- Risk Level: Low
- Detection Tool: Invicti
- CVE: Not Assigned
The login form’s username field allowed browser autocomplete, which can lead to unintended storage and exposure of sensitive credentials on shared or compromised systems.
Why This is a Security Risk
While this may appear to be a minor issue, in high-security environments it presents several risks:
- Credentials may be stored locally in the browser
- Unauthorized users on shared systems may gain access
- Increased risk in case of malware or browser compromise
- Non-compliance with strict security policies and benchmarks
In environments handling sensitive or governmental data, even low-to-medium severity issues must be addressed proactively.
Root Cause
The default WordPress login form does not explicitly disable autocomplete for the username field in certain configurations, allowing browsers to store and suggest previously entered credentials.
Remediation Strategy
To mitigate the issue, we implemented a frontend-level control to explicitly disable autocomplete for the username field.
Implemented Fix
The following script was injected into the login form to enforce secure behavior:
add_filter('login_form_middle', function ($content) {
echo '<script>
document.addEventListener("DOMContentLoaded", function() {
var input = document.querySelector("#user_login");
if(input) {
input.setAttribute("autocomplete", "off");
}
});
</script>';
});Additional Considerations
While disabling autocomplete improves security posture, it should be implemented alongside:
- Strong password policies
- Multi-factor authentication (MFA)
- Secure session handling
- Proper HTTP security headers
Verification
After implementing the fix:
- The vulnerability was rescanned using Invicti
- The issue was successfully mitigated
- No further autocomplete-related exposure was detected
Conclusion
Even seemingly minor vulnerabilities like autocomplete behavior can pose risks in high-security environments. Proper hardening of authentication mechanisms is essential, especially for systems operating under strict compliance requirements.
Need a Security Audit?
If your website or server handles sensitive data, proactive security testing and hardening are critical.
- WordPress Security Hardening
- Server-Level Security (Linux / LiteSpeed / Nginx)
- Vulnerability Assessment & Remediation
? Reach out to DigmLabs for a professional security audit.